Update April 9, 2:40 pm UTC: Telegram denied the existence of RCE vulnerability for Telegram clients, while some security experts claimed it's been a known issue.
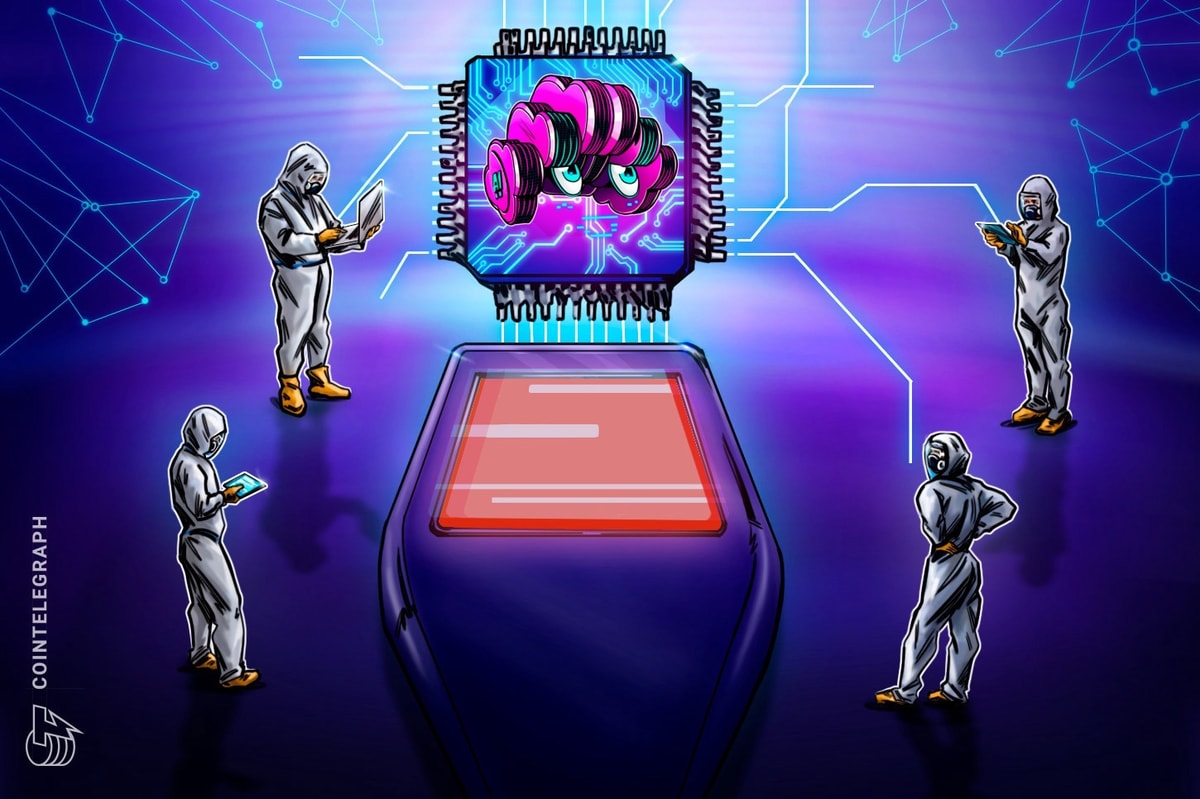
A major vulnerability on Telegram messenger is exposing users to malicious attacks, according to a new report released by the blockchain security firm CertiK.
CertiK Alert took to the social media platform X on April 9 to warn the public against a “high-risk vulnerability in the wild,” potentially allowing hackers to deploy a remote code execution (RCE) attack through Telegram’s media processing.
According to the post, CertiK’s team has discovered a “possible RCE” attack in Telegram’s media processing on Telegram Desktop application.
“This issue exposes users to malicious attacks through specially crafted media files, such as images or videos,” CertiK wrote.
A spokesperson for CertiK told Cointelegraph that the vulnerability is exclusive to the desktop Telegram application because mobile "does not directly execute executable programs like desktops, which generally require signatures." The representative noted that the news on the issue came from the security community.
To avoid the vulnerability, users should check their Telegram Desktop configuration and disable the auto-download feature. The feature can be disabled by going to “Settings” and then tapping on “Advanced.”

“Under the ‘Automatic Media Download’ section, disable auto-download for ‘Photos’, ‘Videos’, and ‘Files’ across all chat types (Private chats, groups, and channels),” CertiK noted.
A spokesperson for Telegram told Cointelegraph that the company "can't confirm the existence of such a vulnerability in Telegram clients."
According crypto enthusiast and grey hat SEO Yannick Eckl, the problem with automatic downloads of media files and RCE attacks in Telegram is not new. "It is a known issue in many, but obviously not all, IT-security circles," Eckl told Cointelegraph.
Telegram is a major cryptocurrency-friendly messenger that allows users to communicate and exchange files and transact cryptocurrencies like Bitcoin (BTC) and Toncoin (TON) using its custodial wallet solution called, simply, Wallet.
The “custodial” part means that Wallet doesn’t give users the private key by default but rather puts the assets in its own custody to help industry newcomers avoid self-custody responsibilities.
Related: Telegram channels eligible for 50% ad revenue, but there’s a catch
The newly discovered vulnerability on Telegram isn’t its first. In 2023, Google engineer Dan Reva found a significant bug that could allow attackers to activate the camera and microphone on laptops running macOS.

In 2021, a security researcher from Shielder discovered a similar media-related issue on Telegram, which reportedly allowed attackers to send modified animated stickers, which could have exposed the victims’ data.
Telegram has been actively addressing potential vulnerabilities on its app, though. Telegram’s bug bounty program has been active since 2014, offering developers and the security research community the opportunity to submit their reports and be eligible for bounties ranging from $100 to $100,000 or more, depending on the severity of the issue.
Magazine: 1 in 6 new Base meme coins are scams, 91% have vulnerabilities